Perimeter Protection for Oil & Gas Facilities: Securing High-Risk Infrastructure in 2026

Why Perimeter Protection Matters in Oil & Gas Facilities Oil and gas facilities face some of the highest security risks of any industrial sector. From unauthorised access and theft to sabotage, environmental risks, and operational disruption, securing the outer boundary of a facility is no longer optional – it is a critical operational requirement. For […]
EVERYTHING YOU NEED TO KNOW ABOUT PERIMETER SECURITY INSTALLATION

Whether you manage a commercial site, an industrial facility, a data centre, utility or critical national infrastructure, one thing is certain – keeping threats on the outside of your boundary is far more effective than dealing with them once they’ve already got in. That is the fundamental principle behind perimeter security installation, and it is […]
PIDS Security for Prisons: Why UK Custodial Facilities Need Advanced Perimeter Intrusion Detection

UK prisons are under unprecedented perimeter pressure. Drone-delivered contraband, sophisticated escape planning, and organised criminal networks probing fence lines have transformed the threat landscape beyond what traditional security measures were ever designed to handle. For prison governors, security managers, and estate directors across His Majesty’s Prison and Probation Service (HMPPS), the message is clear: a […]
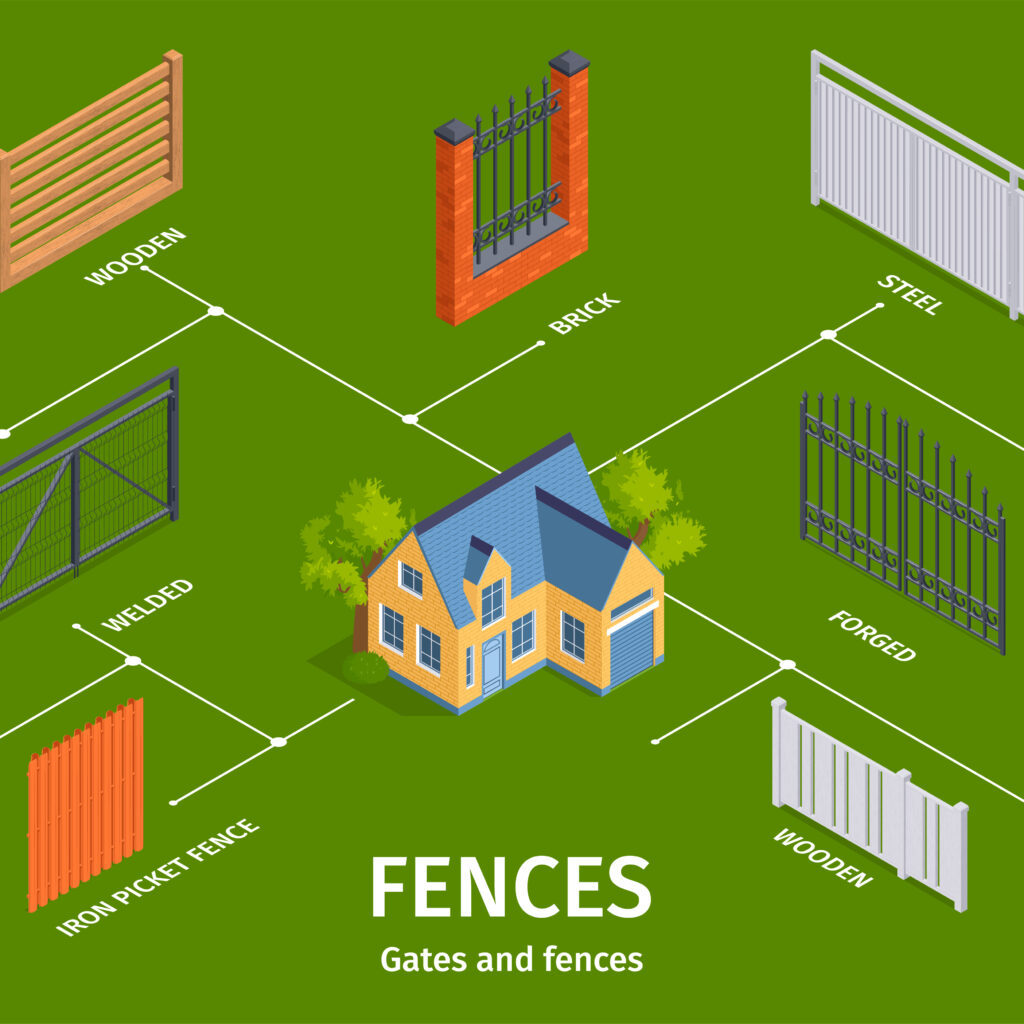
Fence Protection Systems: What Every Property Owner Needs to Know in 2026

Introduction Perimeter security has changed fundamentally. A fence that would have been considered adequate five years ago is now, in many cases, the weakest point of an otherwise well-managed site. Organised criminal groups increasingly target commercial and industrial properties with speed and precision – breaching a boundary, loading a vehicle, and leaving before a response […]
Fence Intrusion Detection & Fence Protection for Transport & Haulage Depots (UK)
Stop Intruders Before They Enter Your Depot A haulage depot can be breached in minutes – but the financial and operational impact can last far longer. Across the UK, transport and logistics sites are increasingly targeted by organised theft, fuel siphoning, and unauthorised access. These incidents rarely involve sophisticated tactics. In most cases, intruders exploit […]
Why Add Perimeter Security to Your Alarm System

In today’s security world, relying solely on internal alarms is no longer enough. Businesses, warehouses, schools, religious places and critical infrastructure sites require proactive protection that stops threats before they reach the building. That’s where perimeter security comes in. By combining your existing alarm with a perimeter security installation, you create a layered defence that […]
Top Commercial Perimeter Security Systems in 2026

Your facility’s outer boundary is its first – and most critical – line of defence. For security managers and facility directors, choosing the right perimeter intrusion detection system (PIDS) can mean the difference between stopping a threat early and dealing with a costly breach. Companies like Sysco Tech are leading the way in providing enterprise-grade […]
A Successful Visit to CLD Systems: EcoPoint Sensors Pass the Test

At Sysco Tech, we are always looking to push our products further – not just in terms of what they can do on paper, but how they perform in the real world, on real installations, against real fence systems. That commitment to rigorous, practical validation is what recently took Mark & Shawn , the Directors […]
How to Secure Perimeter Devices for Intrusion Detection
In today’s world, having robust security at the outer perimeter of facilities is essential. Businesses need to safeguard their assets, employees, and infrastructure from unauthorised access. That’s where advanced perimeter intrusion detection systems come into play, helping organisations keep an eye on activities around their property. These systems offer early alerts, enabling security teams to […]
How Fence Intrusion Detection Is Protecting Utilities and Power Grids
In an era of escalating cyber threats, extreme weather events, and growing geopolitical tensions, the security of utilities and power grids has never been more critical. Yet for all the attention paid to digital and cyber defenses, the physical perimeter – that first line of defense – remains one of the most vulnerable entry points […]
