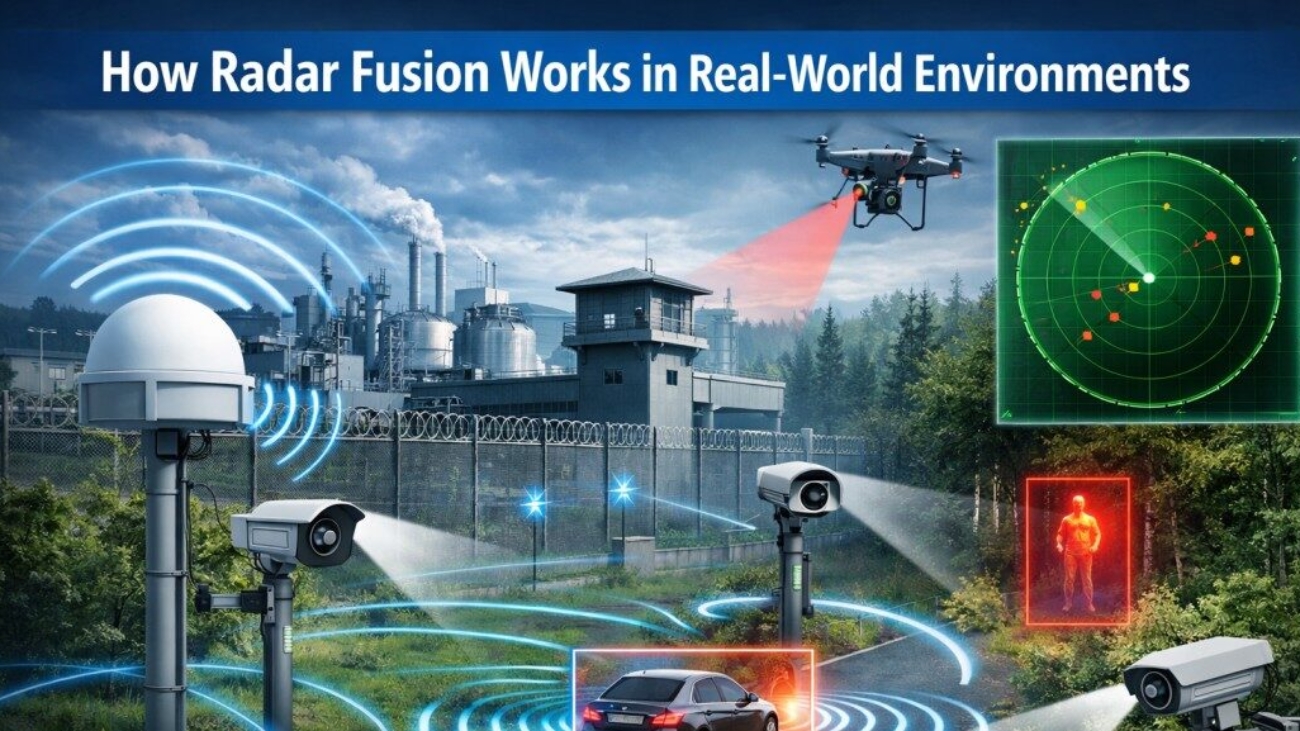
Radar fusion systems work by constantly monitoring the perimeter with radar sensors that reach several kilometres. When the movement occurs, the system immediately signals other sensors (ideally, thermal or PTZ cameras) toward the target.
The magic happens in the software, though. Advanced analytics cross-reference data from various sources, weeding out irrelevant motion, such as wildlife or weather. Only verified threats trigger alerts.
This is essential in realistic UK environments. Heavy rain, mist and low light is standard. The radar’s accuracy does not depend on any of these conditions; detection is simply 24/7.
Upon confirmation of a threat, the system can:
- Alert security teams
- Trigger lighting or audio warnings
- Lock down access points
- Use live video feeds to enable fast intervention efforts
This integrated level of radar fusion is what provides the foundation for contemporary perimeter protection.
Key Components of a Radar Fusion-Based Security System
Radar Sensors
Radar sensors offer a long range of detection and a wide coverage area. They can detect grey movement from open field, coastal and complex terrain, making this suitable for large UK sites.
CCTV and Thermal Imaging
Heat cameras detect thermal signatures, and CCTV provides video verification. And to do so reliably in any light.
AI and Analytics Engines
AI analyses behaviour patterns, distinguishing between humans, vehicles, and animals. Over time, the system learns and improvesits accuracy.
Command and Control Platforms
All data is integrated on one central platform, allowing operators to see, in real time, the entire perimeter.
Why Radar Fusion Is Critical for Next-Gen Perimeter Security Systems
The detection accuracy is greatly improved, along with the operational cost reduction achievable through radar fusion. Automatically validating threats, security teams can work on responding to threats faster and with greater confidence.
Studies show that fusion-based systems:
- up to 95% Improves recognition accuracy
- Lower false alarms by as much as 90%
- Reduce response time by more than 60%
This efficiency is especially important at a time when UK businesses are under pressure from increasing security costs and compliance demands.
Radar Fusion vs Traditional Perimeter Security Systems
The traditional systems are based on independent sensors. Radar fusion brings it all together into a single smart network. Though there is an up-front cost, the long-term savings of fewer false alarms, needing fewer guards and more solid security make it cheaper.
Applications Across UK Industries
Critical National Infrastructure
Hydropower stations, water plants and telecom sites need threat warning as soon as possible.
Commercial and Industrial Sites
Warehouses, logistics facilities and factories gain from area-wide radar coverage.
Airports, Ports, and Transport Hubs
Radar fusion provides safety in large, high-risk areas.
Residential and Gated Communities
Luxury homes employ fusion systems for invisible, dependable security.
The Role of AI in Radar Fusion Security
AI can support predictive threat type analysis, behaviour understanding and learning of the system over time so that a security perimeter does not become itself the weakest link.
Cybersecurity and Data Protection Considerations
Contemporary systems will comply with regulations according to the UK GDPR, they transmit data encrypted and can be hosted in a secure cloud or on-premise.
Challenges and Limitations of Radar Fusion
Radar fusion is powerful, but it must be properly designed, integrated and supported by a skilled workforce. It’s all about the right partner.
Why Radar Fusion Is the Future of Perimeter Security Systems
Smart cities, critical infrastructure investment and a growing threat climate make radar fusion the benchmark for sophisticated security in the UK.
Why Syscotech Is a Smart Choice for Perimeter Security Systems
Sysco Tech provides sophisticated and bespoke perimeter security systems, which have been developed specifically for the UK. Their offerings combine radar fusion, AI analytics and multi-layered detection that effectively safeguard key assets.
Conclusion: Building Smarter, Safer Perimeters
Perimeter security is being reimagined with radar fusion. Bringing together a network of technologies to create one smart system provides organisations with the confidence of accuracy. Investing in the next generation of perimeter security systems is not a choice for UK business and infrastructure; it’s a necessity.
FAQs
1. What is radar fusion in perimeter security systems?
Radar fusion combines radar with other sensors to improve detection accuracy and reduce false alarms.
2. Is radar fusion suitable for UK weather conditions?
Yes. Radar works reliably in rain, fog, darkness, and harsh environments.
3. Are radar fusion systems expensive?
Initial costs are higher, but long-term savings and improved protection deliver a strong ROI.
4. Can radar fusion integrate with existing systems?
Yes. Most solutions are designed to integrate with CCTV and access control systems.
5. Who should consider radar fusion security?
Critical infrastructure, commercial sites, transport hubs, and high-risk properties.